security (49)
Why is the IOT Catnip to Hackers?
The latest developments in IoT security will protect the companies that use them from disastrous hacks
Rob Enderle writing in CIO Magazine May 20 about a new security certification for IOT products lauded the new offering and cited other measures that responsible IoT businesses must take to secure the future of their companies. His opinion piece couldn’t come at a better time.
Those of us watching the IOT “back door” swing open to hackers have been wondering how and when a product certification like this would become industry standard. Underwriter Laboratory’s Cybersecurity Assurance Program (CAP) just might work. But it’s only a start.
The three-level certification process, according to Enderle, will work fine as long as it’s subject to a “rigorous audit process.” However, he also agrees that using a remote network hub with security stopgaps in place (which is what most are doing now) won’t do a thing to protect wireless devices.
Where we are now, where we need to go
During the NXP/FTF Technology Forum 2016, a group of panelists was asked if the Internet of Things was secure yet. What do you think they answered? Yes, they said, no.
Here’s the rub—and the same thing that Enderle writes about: The connected devices in cars, homes, phones need to have specialty security hardware to stop many attacks. Another missing link, according to Global Business Development Manager Damon Kachur at Symantec, is the need to institute “a massive education process compelling security providers to educate consumers on how to operate their devices securely.”
Using cryptography, requiring several rounds of authentication per day, and manufacturers hiring hackers to break into their IoT devices before they put them on the assembly line—these were also solutions that Forum panelists came up with to secure the IoT.
Horror stories averted?
The stories with the highest profiles are those that see connected cars taken over and crashed; cell phones hijacked and set on fire; and that Target breach, when hackers stole credit cards from Target headquarters using the building’s HVAC systems to get in. What else do we need to do, besides work on certification processes and make sure that before we build the next IoT device, we’ve protected it from hackers?
It’s clear that businesses engaged in the IoT revolution need to make security “job one”. There are heartening signs that this indeed is the case. A recent Accenture paper on IOT security claimed that “businesses surveyed by the World Economic Forum identified cyber-attack vulnerabilities as their most important IoT concern.” And an article last month in Forbes reported that venture capitalists are now “following the money” to underwrite cybersecurity start-ups: “Boston-based Lux Research says investment in “cyberphysical” security startups rose 78% to $228 million in 2015, and will increase to $400 million this year. The report cites rapid adoption of IoT tech, with the potential threats it brings in the area of internet connectivity in cars, homes and factories.”
Businesses that are eager to make money on the IOT without being willing to spend the money on securing it will be increasingly prone to customer data breaches and other high-profile disasters that will close their doors—and slow the adoption of IoT devices—and spending—for years to come. Smart companies need to make an investment in securing their latest IoT game changing use-case or product-- or their customers and partners won’t want to make an investment in them.
IoT, as we all know, is not without issues--though we have become reliant upon it in many ways.. In 2015, there were some very viable and tangible proofs that the IoT field is fraught with real peril and that we as IoT designers, developers and companies need to be paying more attention to security. Just how many different IoT companies and arenas were breached? The answer might surprise you-- not to mention terrify you.
Most of us read about the car that was taken over and driven into a ditch. The ramifications of that were clear to all of us, but some even more frightening things have taken place this year..
Did you know that a flight was taken over-- and the man who took over the flight bragged that he had also manipulated the space station?
In the past year, the following hacks have taken place.
Medical devices--The FDA ordered that specific drug pumps be no longer used. The software was bad enough that hackers could change the dosage being delivered to people who were using them.So we have the possibility of murder by internet??http://www.securityweek.com/fda-issues-alert-over-vulnerabl…
The DOE--According to a June 2015 Congressional Research Service (CRS) report, hackers successfully compromised U.S. Department of Energy computer systems more than 150 times between 2010 and 2014. "Records show 53 of the 159 successful intrusions were "root compromises " "http://www.usatoday.com/…/cyber-attacks-doe-energy/71929786/
A Steel Mill --An entire steel mill was breached resulting in "massive destruction of equipment" http://www.wired.com/…/…/german-steel-mill-hack-destruction/
The US National Nuclear Security Administration--The people who are responsible for managing and securing the entire nation's nuclear weapons stockpile, experienced 19 successful cyber attacks during the four-year period of 2010 - 2014
Firearms--TrackingPoint makes a smart rifle--what it does is to digitally "tag" a target, and then locks the trigger until the gun is perfectly positioned to hit it --and it can hit up to half a mile away but... now there has been a serious flaw found in the software so that a hacker could make a law enforcement hit the hostage rather than the intended target.http://money.cnn.com/2015/07/29/technology/hack-smart-rifle/
Offshore Oil Rigs --Hackers have also shut down an oil rig by tilting it sideways..They hit another rig so hard with malware it was not seaworthy for 19 days..
Government Buildings Department of Homeland Security recently disclosed that hackers had managed to penetrate a state government facility and a manufacturing plant in New Jersey--now all they did was change the temperature, but what COULD they have done.. really think about that.
Last.. but not least.. go ahead and buy that cool toaster and refrigerator..... a funny thing happened with hundreds of kitchens in the UK. All of tehm were hacked and the resultant hack wouldn't allow them to make certan kinds of food in their toaster or store it in their fridge.http://www.cbronline.com/…/iot-security-breach-forces-kitch…
IOT is a time saver and offers us incredible convenience, but as we're beginning to find out, there are some real ramifications to the use of IoT devices that we need to be aware of. More to the point, companies and industries who are offering these devices need to take full responsibility to assure the security of the devices they are offering. IoT security workers and developers are more important than ever before..
For more information about IOT and Security check out our new websitewww.internetofthingsrecruting.com - Need to update you IOT Security Team - Click Here to schedule a free IOT Needs Assessment Call.
The Internet of Things (IoT) concept promises to improve our lives by embedding billions of cheap purpose-built sensors into devices, objects and structures that surround us (appliances, homes, clothing, wearables, vehicles, buildings, healthcare tech, industrial equipment, manufacturing, etc.).
IoT Market Map -- Goldman Sachs
What this means is that billions of sensors, machines and smart devices will simultaneously collect volumes of big data, while processing real-time fast data from almost everything and... almost everyone!!!
IoT vision is not net reality
Simply stated, the Internet of Things is all about the power of connections.
Consumers, for the moment anyway, seem satisfied to have access to gadgets, trendy devices and apps which they believe will make them more efficient (efficient doesn't necessarily mean productive), improve their lives and promote general well-being.
Corporations on the other hand, have a grand vision that convergence of cloud computing, mobility, low-cost sensors, smart devices, ubiquitous networks and fast-data will help them achieve competitive advantages, market dominance, unyielding brand power and shareholder riches.
Global Enterprises (and big venture capital firms) will spend billions on the race for IoT supremacy. These titans of business are chomping at the bit to develop IoT platforms, machine learning algorithms, AI software applications & advanced predictive analytics. The end-game of these initiatives is to deploy IoT platforms on a large scale for;
- real-time monitoring, control & tracking (retail, autonomous vehicles, digital health, industrial & manufacturing systems, etc.)
- assessment of consumers, their emotions & buying sentiment,
- managing smart systems and operational processes,
- reducing operating costs & increasing efficiencies,
- predicting outcomes, and equipment failures, and
- monetization of consumer & commercial big data, etc.
IoT reality is still just a vision
No technology vendor (hardware or software), service provider, consulting firm or self-proclaimed expert can fulfill the IoT vision alone.
Recent history with tech hype-cycles has proven time and again that 'industry experts' are not very accurate predicting the future... in life or in business!
Having said this, it only makes sense that fulfilling the promise of IoT demands close collaboration & communication among many stake-holders.
A tech ecosystem is born
IoT & Industrial IoT comprise a rapidly developing tech ecosystem. Momentum is building quickly and will drive sustainable future demand for;
- low-cost hardware platforms (sensors, smart devices, etc.),
- a stable base of suppliers, developers, vendors & distribution,
- interoperability & security (standards, encryption, API's, etc.),
- local to global telecom & wireless services,
- edge to cloud networks & data centers,
- professional services firms (and self-proclaimed experts),
- global strategic partnerships,
- education and STEM initiatives, and
- broad vertical market development.
I'll close with one final thought; "True IoT leaders and visionaries will first ask why, not how..!"
Guest blog by Bill Graham, follow him here. The post was originally posted here.
Every IoT and embedded device manufacturer endeavors to field secure and safe products. However, even with the robust development processes, it's difficult to ensure complete security in finished products more so in legacy products. As the ever-expanding IoT marketplace puts a bigger emphasis on embedded device security, better techniques are required to improve security. I wrote a blog series this fall on improving IoT security with source-based static analysis and binary static analysis coupled with software hardening, but I focused primarily on the static analysis part of the equation. GrammaTech's software hardening techniques complement our static analysis know-how to greatly improve the current and future robustness of embedded software.
Binary Analysis and Static Rewriting
Analyzing application binaries allows GrammaTech's rewriting tools to discover the use of potentially problematic code patterns, libraries, or OS functions. The rewritten binaries have wrappers around such code to prevent erroneous behavior. For example, function call stack usage can be instrumented to prevent stack overflow and subsequent code injection. Another example would be preventing calls to known problematic library functions like strcpy() from causing buffer overflow errors.
Rewriting a binary executable into a robust hardened version provides quality and security assurance for any version of the application -- current and future versions are protected.
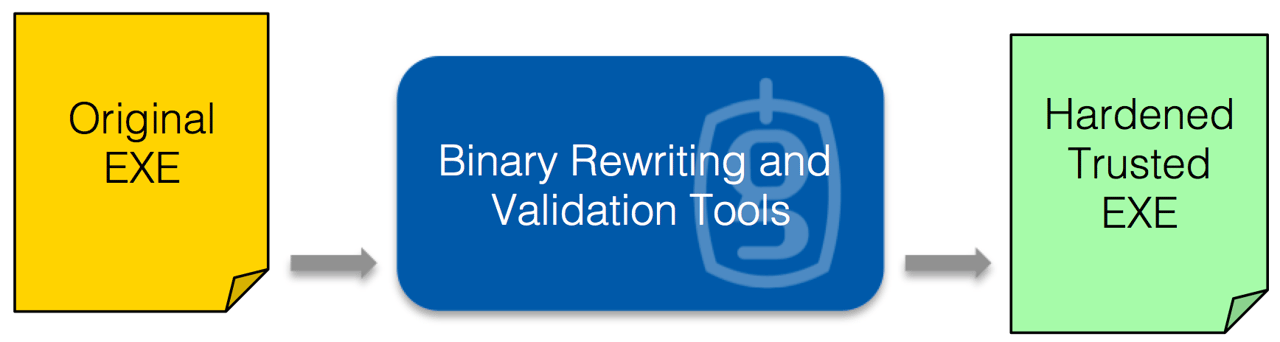
GrammaTech's hardening tools static rewrite binaries into more robust and secure applications.
Confinement and Diversification: Binary Rewriting Techniques
The goal of confinement is to prevent undetected vulnerabilities from causing a failure in an executing application. Techniques to detect and prevent certain specific classes of vulnerabilities already exist to some extent, but often lead to a program failure state -- which, in turn, leads to a denial of service. Although an attack might be prevented, these consequences are unacceptable in critical systems. GrammaTech has been researching sophisticated confinement techniques that allow applications to detect the same kinds of attacks, but continue operation (while still containing the vulnerability). Combining binary analysis to detect the potential vulnerability with static rewriting to confine the exploit, it's possible to greatly reduce and even eliminate the impact.
Diversification techniques are used to alter the default code and memory layout to prevent potential exploits. By rearranging the subroutine calling sequence, stack, heap, and global data layout, it's possible to prevent vulnerabilities from being exploited. Stack overflow errors that lead to code injection exploits, for example, can be thwarted with these techniques.
Protection Now and in the Future
Binary analysis and rewriting by nature doesn't require source and is version-independent. As such, IoT device manufacturers can use GrammaTech's hardening techniques on every release of their applications, making software hardening a standard procedure in the software release process. In doing so, organizations can assure better robustness and security for even minor upgrades, without huge re-testing costs.
CONCLUSION:
Security defines the success of IoT. Good software development techniques are a good start, but adding software hardening is even better. GrammaTech's software hardening techniques provide version-independent protection from vulnerabilities and runtime errors while maintaining system functionality. In addition to the improved security and safety provided, software hardening offers compelling reductions in cost, risk, and time savings.
In the 1996 sci-fi blockbuster movie “Independence Day”, there is a comical seen near the end where actor Jeff Goldblum, playing computer expert David Levinson, writes a virus on his Macintosh PowerBook that disables an entire fleet of technologically advanced alien spaceships. The PowerBook 5300 used in the movie had 8 MB of RAM. How could this be?
Putting aside Apple paying for product placement, we’re not going to stop advanced alien life who are apparently Mac-compatible.
I cite the ridiculous Independence Day ending because I was recently reading through a number of IoT security stories and began thinking about the implications of connecting all these things to the network. How much computing power does one actually need to hack something of significance? Could a 1997 IBM Thinkpad running Windows 95 take down the power grid in the eastern United States? Far fetching, yes, but not ridiculous.
Car hacks seem to be in the news recently. Recall last month’s Jeep hack and hijack. Yesterday, stories came out about hackers using small black dongles connected to a Corvette’s diagnostic ports to control many parts of the car through, wait for it, text messages!
Beyond cars and numerous other consumer devices, IoT security has to reach hospitals, intelligent buildings, power grids, airlines, oil and gas exploration as well as every industry listed in the IRS tax code.
IBM’s X-Force Threat Intelligence Quarterly, 4Q 2014 notes that IoT will drag in its wake a host of unknown security threats. Even IBM, a powerful force in driving IoT forward, says that their model for IoT security is still a work in progress since IoT, as a whole, is still evolving. They do suggest however five security building blocks: secure operating systems, unique identifiers for each device, data privacy protection, strong application security, strong authentication and access control.
In the end, it will be up to manufacturers to build security from the ground up and continual work with the industry to make everything more secure. As we coalesce around an ever evolving threat landscape, it will be the responsibility of smaller manufacturers, giants like IBM and industry organizations like the Industrial Internet Consortium and Online Trust Alliance’s IoT Trust Framework to help prevent the ridiculous from happening.